What Happened?
Utah Valley Eye Center in Provo, UT reported on Oct 31, 2019, that their scheduling system was compromised. The compromise occurred on June 18, 2018.
The attacker used the information they were able to gather to send phishing emails to the patients. The attacker sent emails disguises as PayPal emails to compromise PayPal accounts.
According to the Utah Valley Eye Center, the attacker was able to obtain 5764 email addresses and other PII (Personally Identifiable Information) such as a home address, phone numbers, birth dates, and names. It is reported that PHI (Protected Health Information) was not accessed by the attacker.
Utah Valley Eye Center did report the breach to the required authorities and did send a notification to all 20,418 patients alerting them to the attack as a precaution. The patients were advised to place a fraud alert on their credit files.
 What Could Have Been Done Differently?
What Could Have Been Done Differently?
There are two things that could have been handled differently in this case.
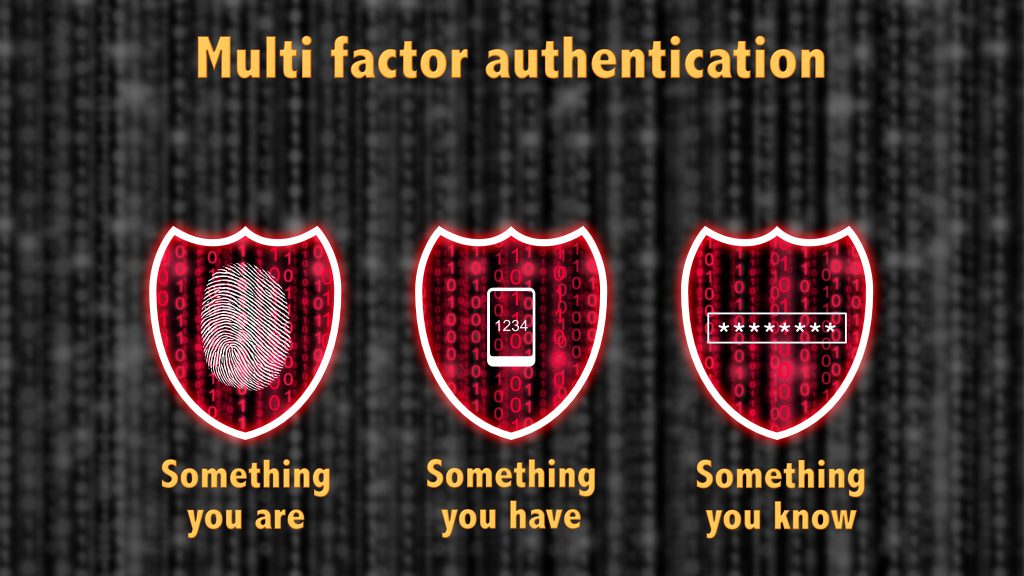
- MFA was likely not set up on the scheduling system. It’s not clear if that was an option with the scheduling system but it should be. If it was the eye doctor should have enabled and used it accordingly. This would have most likely prevented the breach.MFA is short for multi-factor authentication. Essentially, it’s a second form of authentication and can be a pin sent via SMS (not recommended), soft token or biometric, or any combination of these. Some portals can also be configured to only allow login from specific locations.
- There is a big gap in time from the compromise to the notification. The breach occurred on June 18, 2018, but was not reported until October 31, 2019. That’s more than 16 months.It’s not clear when the eye doctor became aware of the compromise but if the attacker was in the system for 16 months, they would have probably gotten a lot more than 5764 email addresses.
It’s important to understand that notification of breaches need to be reported in a reasonable amount of time. Since it appears PHI was not accessed the 60-day rule is not relevant, but most states have a law that data breaches are to be reported within a few months.
I was unable to find anything that states how long a business must notify the appropriate parties of a breach. In Connecticut, it’s 90 days.
Utah can also fine $2500 per consumer up to $100,000. In this case, Utah Valley Eye Center is looking at the maximum penalty.
Because the records include more than one personally identifiable piece of information Utah Valley Eye Center is subject to the rules of notification and fines.
The Potential Cost
It looks like Utah Valley Eye Center can be fined $100,000. Since the breach was just reported a fine has not been levied yet.
They could potentially be fined for delayed notification as well if Utah has laws regarding the time frame for notification of a breach.
It’s not clear if PHI was impacted. According to most sources, it was not but this breach is on the HIPAA Wall of Shame which means the OCR is investigating. If PHI is included in the breach the fines can be much more significant.
While not likely to be this high when all is said and done, and if it is determined that PHI was accessed, Utah Valley Eye Center can be looking at over $8,000,000 in fines and costs to mitigate.
 The Lesson
The Lesson
The attack looks to be somewhat amateurish based on the information available. A weak password, a little social engineering, and lack of MFA and anyone can easily compromise an online portal.
From there it’s easy to grab email addresses and other PII. There are freely available tools on the internet to create phishing emails disguised as PayPal. They even help you clone the PayPal site.
To avoid all this the following should have been in place:
- Use Complex Passwords/Passphrase (Upper, lower, numbers, special characters)
- Educate Your Staff on Social Engineering
- Enable MFA – Avoid SMS if possible
- Enable Logins from Specific Location/IP Address
If the scheduling portal does not have these options, it’s time to move on to another scheduling portal. While it would be hard to believe
While there is no evidence that PHI was involved in this breach the OCR is still investigating. Even if they determine that no PHI was breached, they will likely scrutinize Utah Valley Eye Center’s HIPAA compliance program. Other healthcare providers have been fined by the OCR for lax compliance programs in the past. Utah Valley Eye Center could be on the hook for more than the $100,000 fine for having PII breached.
To Read Our Previous HIPAA Breach Case Study Click Here
Read About the Breach Here and Here.



We should always be careful about our sensitive information online. Thanks for the great tips!
That is going to be a very hefty fine. They should have taken much better care of their security.
Oh man that is so scary, we all need to be oh so very careful. Thanks so much for sharing this with all of us!
This is certainly scary! That’s going to be a massive fine on their part. It just goes to show how important security is!
Protecting our information is so crucial. Thanks for sharing your knowledge.
It is so important to follow the guidelines. That would avoid a lot of these cases to start with. Thank you for the info.
I like that this post is both informative and also a way to remind us all to be careful with handling and recieving Information.
Always be sensitive about what information you are giving out!
This is a very steep fine. Eye Centers like this one need to be more careful with their systems and security.
It continues to amaze me that there are people out there who think it is fun and time well spent trying to hack into the systems of well established as well as new organisations. Can someone not give these people something constructive to do with their time?
Your posts are always so informative and helpful, it’s so important to protect our information online.
being ignorant doesn’t save us from things like this. thanks for sharing this information. it’s indeed scary when it comes to our privacy being invaded…
Cha at Little MisadvenCHA
A data breach like this one can be terrifying for the patients. You always want to think twice about the information you share.
It’s crazy how easily our information can be revealed. This is a great case study.
Sometimes we don’t realize how important it is to keep our information safe. Thanks for sharing this great information
Thanks for sharing this case study. We should be careful about sharing information online.
I remember my parents getting a notice about a breach happening with a medical facility in our local area. It was crazy to think that they weren’t doing a better job of protecting patient info.