
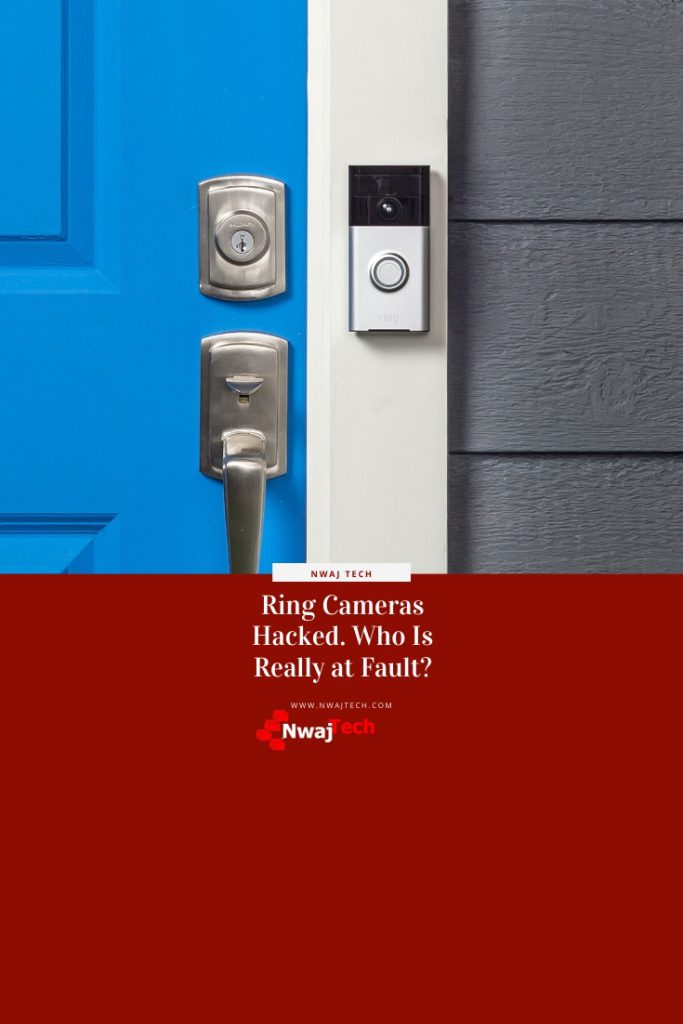
Ring Cameras Hacked. Who Is Really at Fault?
It has been all over the news the last few days. Almost every news title is something along the lines of “Ring Cameras Hacked Causing Hysteria in Households”.
There’s no doubt that the cases where this happened are scary. Videos have surfaced on the internet of someone talking to children and other family members through a ring camera.
Imagine purchasing a camera to help with keeping your family secure only to have strange adult men talking to your children through them. I’d be very uneasy with it. I would lose sleep. I already do lose sleep thinking about my client’s and family’s security.
But who’s really to blame?
Credential Stuffing 101
I’m going to separate the media into two groups.
The responsible media that reports the story accurately and the irresponsible group that reports what will get you to click.
The responsible group includes terms like credential stuffing.
This is great but what is credential stuffing?
To understand password stuffing you first must understand one part of the dark web.
The dark web is like the black market on the internet. One of the items you can purchase on the dark web is lists of usernames and passwords often uncovered during previous data breaches.
For example, in 2012 117 million emails and passwords were breached on LinkedIn (reported in 2016). This list is still used today to compromise other accounts on the internet.
Attackers (I refuse to call them hackers) use these lists to try the compromised credentials on other websites and online resources.
Many people likely used the same credentials for LinkedIn and Facebook for example. If you did then the attackers would successfully access your Facebook account with the credentials purchased on the dark web.
 What Does That Have to Do with Ring Cameras?
What Does That Have to Do with Ring Cameras?
Ring cameras are accessible over the internet to the end-user. Once the ring camera is connected to your network you can connect to them remotely through an app or website to view the camera feed and interact with anyone that is in view of the camera.
You have probably seen the commercials of the homeowner scaring off would-be criminals by talking to them through their ring doorbell. The premise is similar to a ring camera but there are obviously other use cases.
Some ring camera owners use their cameras to talk to their pets while they’re not home. Others might use them to communicate with the kids when they get home from school.
There are lots of positive uses for ring cameras.
With ease of use comes risk.
All these features are great, but they come with an inherent risk. Anything that is exposed to the internet has the potential for compromise. Ring cameras and other IoT devices are no exception. In fact, they are more at risk than computers and servers.
IoT devices tend to be less security-focused than enterprise and commercial computer systems. They are not typically developed with security in mind.
Ring Cameras, however, are the exception to the rule.
Amazon is the company behind Ring Cameras. The well-publicized attacks utilizing Ring Cameras are not the fault of Amazon or the cameras.
Who Is at Fault?
As was the case of the Disney+ accounts being compromised the end-user is at fault here.
It was reported that every case of a Ring Camera being compromised credential stuffing was used. In other words, someone grabbed usernames (emails) and passwords and gave it a try on the Ring Camera app or website.
In a lot of cases, they failed but in some they did. Those Ring Camera users reused credentials that were available on lists on the dark web.
The end-user is at fault for not using a more complex password policy that includes not reusing passwords.
They may not know better or they simply didn’t consider the risk, but the successful attacks are the result of not taking care to be more secure with password usage.
Beyond a better password policy, TFA (Two-Factor Authentication) can also be enabled. Whenever TFA/MFA is an option you should use it. Utilizing this could have mitigated the weak password and avoided the problem altogether.
 Security Should Give You Peace of Mind
Security Should Give You Peace of Mind
Many years ago, I lived in a small apartment on the first floor of an apartment building. I used to work until 2 am. One night I came home to find my bathroom window open, the curtain knocked down and a small TV I had in my bedroom missing.
I came to learn I interrupted someone as they were breaking into my apartment. As you can imagine this is a little unsettling.
I can imagine how it must feel to have your private home life broken into through a device intended to make it more secure.
Security is top of everyone’s mind but often suffers because we also want things to be easy.
Security is Everyone’s Responsibility.







This is scary! I plan on getting a Ring, but I’ll set it up as a two step authentication so it won’t be hacked.
I always make my parents read your blogs because they always find them infinitely useful …
People just need to be smarter and things like this won’t happen. We plan on eventually getting a Ring but will do a better job of making sure it’s secure. Thanks so much for sharing this with all of us!
Wow, it’s crazy that these attacks keep happening, but I guess we have to be smarter too with our password choices!
Wow! I’ve heard about baby monitors being hacked, but not about ring cameras. I’m shocked, because sometimes I reuse my usernames. After reading this I realized that I’m exposing myself. I’m going to be more careful and creative from now on.
I am going to be moving soon, so I won’t have a ring for a while yet. I am waiting until I move to the next house. But this is a great warning for me. Thank you!
I didn’t know about this at all but it’s scary. I was going to get a doorbell camera but maybe I’ll not bother. Sometimes too much technology can be a bad thing.
I downloaded a 2 factor authentication now on my ring. I do love the way it works and how I can see everything.
This is proper scary. I was thinking of getting these cameras but won’t for now. Can’t believe they got hacked.
I have a Ring at my house. It is kind of nerve wrecking these can get hacked into.
I don’t have this at our house and this is something that I really need for safety purposes. Thanks for sharing this.