
5 Reasons CT Municipalities Have a Huge Ransomware Target on Them
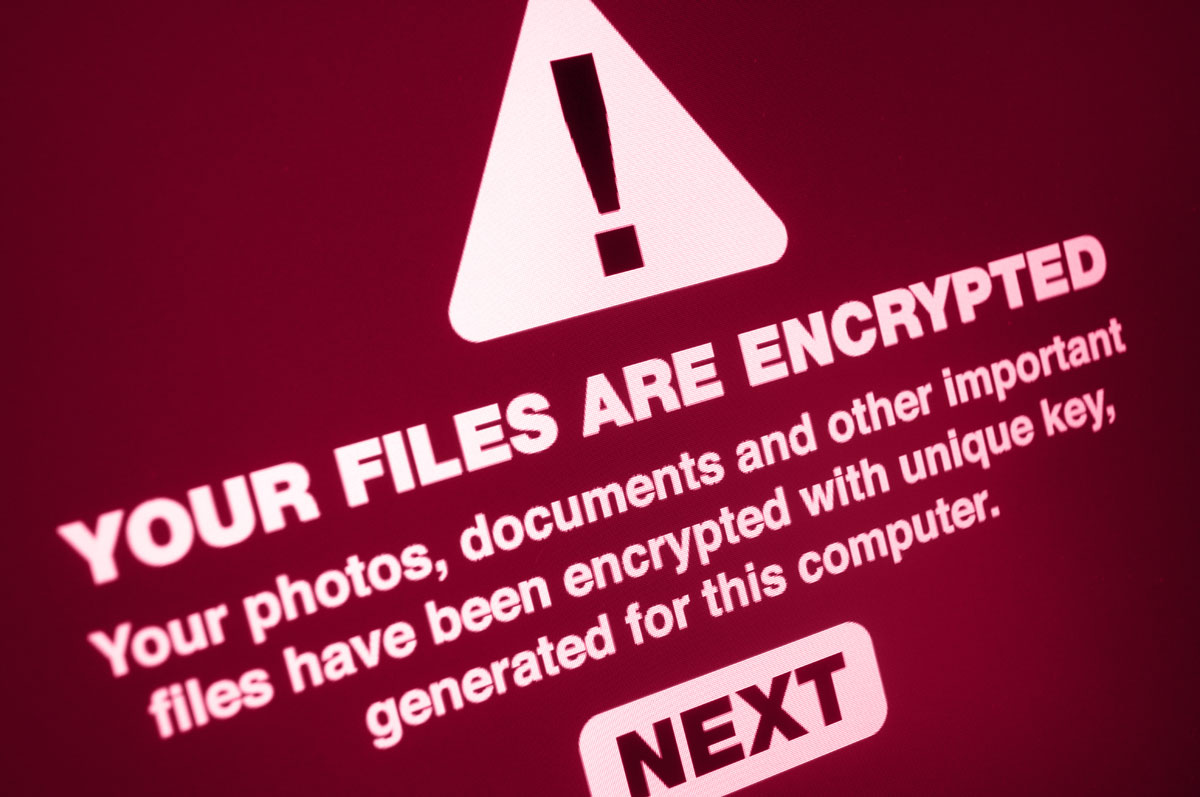
It’s been an extremely tough 2019 in the Cyber Security front. Ransomware attacks have increased by more than double in the first quarter of 2019. Record ransoms are being paid and, in some cases, businesses are opting to close rather than pay the ransom and deal with the fallout.
In some industries ransomware attacks have increased threefold or more in the first quarter of 2019. Phishing attacks are targeting EVERYONE.
Of course, we pay attention to the trends in large part to protect our clients. We also like to keep them aware of what is going on.
One trend that we are paying close attention to is the dramatic increase in ransomware attacks on town municipalities and the increase in the size of the ransom.
Here are Just Some of the Most Recent Ransomware Attacks on Local City Governments.
Baltimore was still impacted more than a month after a ransomware attack. Baltimore chose to not pay the ransom. We agree with this policy. Typically paying the ransom means you will be targeted again. There’s also no guarantee that paying the ransom will get your files decrypted.
The month of June was a tough one for towns in Florida. At least three local Florida governments were hit with ransomware. The ransoms ranged from $460,000 to $600,000. In each case, the attack began with an employee clicking on a link in an email (Phishing).
In the beginning of July, the Georgia court systems were hit by a ransomware attack. Georgia is no stranger to ransomware attacks having been victimized a few times over the last two years.
Mayors across the US have stated that local governments need to refuse to pay ransoms going forward. This article states that there have 22 major ransomware attacks on local governments in 2019.
Paying a ransom makes you a more attractive ransomware target in the future. Some CT municipalities have already paid ransoms as noted below.
 Connecticut Municipalities Ransomware Attacks In 2019
Connecticut Municipalities Ransomware Attacks In 2019
You’re probably wondering what that has to do with Connecticut town government ransomware attacks.
In October of 2018, the town of West Haven paid a $2000 ransom to decrypt their files. So far in 2019 Plymouth and Colchester have been victimized by Ransomware. In Plymouth, it was determined that the ransomware originated from an email (Phishing).
In January 2019 the Bridgeport school system was hit with a ransomware attack.
Connecticut is no stranger to ransomware attacks. Healthcare Systems, local businesses, and town municipalities have all become victims of hackers seeking to make a quick buck.
But Why are Municipalities at Risk of Ransomware Attacks?
5 Reasons Connecticut Municipalities Have a Huge Ransomware Bullseye on Them
Why are municipalities such huge targets for ransomware? We’ve come up with 5 reasons Connecticut municipalities are potential high targets for hackers.
Does your town fall into any of these categories? If so, your town is at risk.
-
No Formalized Phishing Prevention or Awareness Training
In most of the cases listed in this article, the entry point for the hackers was through a phishing email.
Phishing has gotten a lot more sophisticated over the last few years. It is harder to recognize by most people today thus making it a more appealing approach for hackers.
EVERY business should have a phishing mitigation plan in place. That plan needs to include proactive phishing email alerts, education, and testing.
-
Lack of BCDR Makes Your CT Municipality a Ransomware Target
Business Continuity/Disaster Recovery – Nwaj Tech offers Business Continuity/Disaster Recovery services that can have you back up and running within minutes.
This is accomplished through a system of backing up your critical systems locally and to the cloud. The system is virtualized and available for use in the event your physical (or cloud-based) system is attacked.
Your downtime is minimized to minutes rather than days or weeks. Remember, Baltimore was now back to 100% for over 6 weeks. While refusing to pay the ransom is a good strategy how much was lost to downtime as a result of not having a BCDR plan in place?
Aside from the BCDR options we offer having a good backup of any critical systems is important to your municipality not being the victim of a malicious attack.
-
Outdated Software Increases Risk
This always seems like a no brainer but it’s a serious problem. As of June 2019, almost 42% of the Windows computers worldwide were not using Windows 10.
Almost 32% of those computers are running Windows 7. Windows 7 computers are at a much higher risk of being a ransomware target.

Microsoft will stop support for Windows 7 in just over 5 months (January 2020). That means unless you have a plan in place to update to Windows 10 you are at risk.
One of the more recently discovered ransomware attacks targeted a vulnerability in Windows 7 and Windows Remote Desktop Protocol.
You may remember WannaCry from last year (2018). WannaCry almost exclusively attacked Windows 7 systems.
It’s not just operating systems. Browsers, Adobe and Microsoft productivity suites, Java and many other software utilities need to be updated almost always to address security issues.
-
Relaxed Policies
I am not suggesting you need to be a tyrant but when I walk into a town hall and one employee is on Facebook, 3 other computers are left unlocked with no one on them, and there are no privacy screens on any of the computers I cringe. You become an instant ransomware target in my opinion.
What often happens is policies are created but never truly enforced until the inevitable happens. This causes a lot of finger-pointing and unnecessary discussions when a malware attack occurs.
The policies are not new and need to be enforced to prevent social engineering of any kind. Social engineering almost always leads to some type of theft.
-
Inadequate Malware Protection Makes You a Ransomware Target
Many of the more well-known anti-malware protection suites are reactive. They look for signatures to identify malicious content.
The problem with this approach is that hackers and attackers know this. Changing a few lines of code in a malware package will make it unrecognizable to the security software looking for signatures of the malware package.
Anti-malware software updates are almost always to address new malware variants. In other words, the bad guys are one step ahead of the good guys.
New proactive malware protection is available. These behavior and anomaly-based packages proactively look for things that are out of the ordinary. When they find potentially malicious software, the anti-malware suite temporarily quarantines the files/scripts until a tech can review them.
There’s No Time to Stop Ransomware
One of the greatest problems facing the technology world is the lack of support. There are less qualified IT professionals, especially cybersecurity professionals than there are positions. Municipalities, especially smaller ones, are already struggling to find the time to hire a qualified IT team, budget and get their staff trained for awareness.
This makes CT municipalities appealing ransomware targets.
An MSP like Nwaj Tech can handle all of this and more while keeping the IT budget lower than it would be if you hired internally.
Towns of Connecticut. Don’t be the next headline in the local or national news. All it takes is one email to end up with a $500,000 ransom. Without proper mitigation and training, it’s not if, it’s when.
Get our free ebook “Ransomware & Office365”




I live in Georgia and I’d heard about ransomware attacks here. I had no idea how widespread it was. We need to be prepared for it and now I’m wondering if I’m protected enough.
I just read this morning that a town in Indiana was hit with ransomware.
It seems insane to me that large agancies wouldn’t be better protected from online attacks…. Though, it shouldn’t surprise me that much because as a part of my Master’s degree, I did my final thesis paper on the Computer Fraud and Abuse Act which Congress hasn’t updated since it was enacted in the 80’s and was only really enacted since they were afraid of the movie “War Games”.
Yikes, I always worry about these. I’ve heard about them, and so far I’ve been lucky, but I am always cautious. I tell my kids to be cautious too.
I agree with you that there needs to be more prevention in place. In my opinion, workers shouldn’t be allowed to access social media or personal email during the workday at their place of work. It is highly disruptive and can now be a safety issue. There should be training in place and consequences when employees do not follow protocol. This stuff will just continue to get worse if human error isn’t addressed.
Yikes. that’s pretty scary. My company is all about protecting itself from cyber attacks, thank goodness.
This is always good information to know. It is crazy that they target us and I worry about my safety.
It is very scary. Are we ever safe ? It is so sad we have to have these things happen.
Yikes. We all know these things happen, but reading about it here sheds more light on it, and it’s pretty scary. There should definitely be more prevention put in place and policies that govern how employees use their work computers should be enforced.
I am totally worry about our safety. Thanks for sharing such an useful information
It’s crazy that these days people don’t know better than leaving their computers unlocked and clicking on random links in their emails, especially on official institutions. Maybe the municipalities should train their employees not to do this.
We should really be responsible on how we use computer. Be mindful especially when clicking links.
I come from 18 years working in the IT, software and hardware sector and this is such a reality for so many companies. You encourage them to purchase protection and they don’t think it is important until something happens. Paying $400,000 to $600,000 to these hackers is just plain ridiculous.
This is alarming. The prevalence of ransomware attack against these agencies should be a major source of concern for the government and the public alike. Thank you for raising awareness about this matter.
Wow ransomware is scary. This was an informative post and just learning more about this dangerous hacking system.